Security & Cybersecurity Courses
Keeping yourself, your users, and your data safe is important no matter what language or technology you use. Understanding what kinds of attacks exist and how to mitigate or prevent them will give you more control and peace of mind.
- Most Relevant
- All Types
-
All Topics
- All Topics
- • AI
- • Vibe Coding
- • JavaScript
- • Python
- • No-Code
- • React
- • Coding for Kids
- • Design
- • HTML
- • CSS
- • Game Development
- • Data Analysis
- • Development Tools
- • Databases
- • Security
- • Digital Literacy
- • Swift
- • Java
- • Machine Learning
- • APIs
- • Professional Growth
- • Computer Science
- • Ruby
- • Quality Assurance
- • PHP
- • Go Language
- • Learning Resources
- • College Credit
- Reset filters
-
Introduction to Application Security
Welcome to the realm of web security, where millions of dollars and people’s liv...
- Security
- Intermediate
- 72 min
-
(UPI) Chapter 17: Blockchain Security Analysis
In this chapter, the discussion provides a comprehensive analysis of blockchain ...
- College Credit
- Beginner
- 38 min
-

Security Literacy
The internet is an invaluable resource for information and entertainment, but it...
- Security
- Beginner
- 83 min
-
Working with $_GET and $_POST in PHP
This course will show you how to work with PHP Superglobals such as $_GET and $_...
- PHP
- Intermediate
- 44 min
-
(UPI) Chapter 8: Cybersecurity of Critical Infrastructure
In this chapter, the analysis centers on the cybersecurity of critical infrastru...
- College Credit
- Beginner
- 34 min
-

Introduction to Data Security
Keeping data and communications secure is one of the most important topics in de...
- Security
- Beginner
- 48 min
-
(UPI) Chapter 1: Basic Concepts and Models of Cybersecurity
Chapter 1 of the cybersecurity book introduces the foundational concepts and cha...
- College Credit
- Beginner
- 60 min
-
(UPI) Chapter 15: Cyber-Security Training and Continuous Adaptation of Programmes
In this chapter, the focus is on cybersecurity training and the continuous adapt...
- College Credit
- Beginner
- 47 min
-
(UPI) Chapter 2: Core Values and Value Conflicts in Cybersecurity
This chapter explores the fundamental ethical values in cybersecurity, including...
- College Credit
- Beginner
- 40 min
-
Internet Street Smarts
The Internet Street Smarts course by Cyber Collective empowers learners to navig...
- Security
- Beginner
- 26 min
-

Using Cookies and JWTs for Secure Authentication
Refactor an existing authentication project by using cookies and JSON Web Token ...
- PHP
- Advanced
- 71 min
-
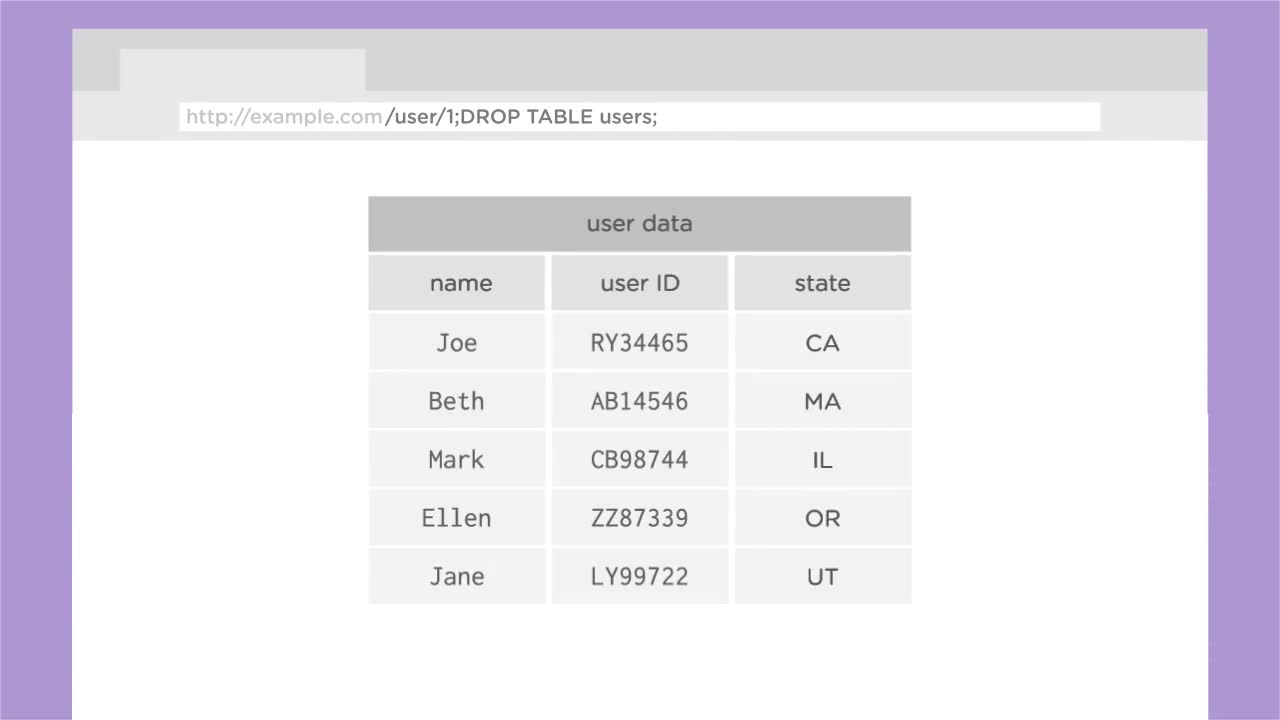
PHP & Databases with PDO
Whether you have aspirations of working on a Content Management System, an E-Com...
- PHP
- Beginner
- 88 min
-

PHP User Authentication
Learn how to implement a custom user authentication system that controls users a...
- PHP
- Advanced
- 157 min
-
(UPI) Chapter 4: Cybersecurity and the State
In this chapter, cybersecurity and the state are examined with a focus on how bo...
- College Credit
- Beginner
- 36 min
-
(UPI) Chapter 7: Cybersecurity in Health Care
In this chapter, the discussion centers on the ethical, moral, and technical dim...
- College Credit
- Beginner
- 28 min
-
(UPI) Chapter 5: Norms of Responsible State Behaviour in Cyberspace
In this chapter, we examine the evolving norms of responsible state behavior in ...
- College Credit
- Beginner
- 36 min
-
(UPI) Chapter 12: Threat Detection and Defense Techniques
In this chapter, the discussion centers on advanced threat detection and defense...
- College Credit
- Beginner
- 39 min
-

Introduction to Algorithms
Algorithms are a fundamental topic in computer science, power many of the large...
- Computer Science
- Beginner
- 134 min
-

The Treehouse Show
The Treehouse Show is our weekly conversation with the Treehouse Community.
- HTML
- 339 min